What Qualifies as ‘Trade Secrets’?
What is — and is not — confidential, proprietary or protected data? Trade secrets can include company financial records; pricing information; client or customer lists; and patentable designs, processes, formulas, especially those in connection with a unique manufacturing process.
Information, lists or other content publicly available for free or a fee generally do not qualify as trade secrets. Content becomes proprietary if it has been refined or culled to create momentary value or to create an economic or market advantage over the competition.
Tech support teams have a saying: There are two types of computer users — those who have been hacked, and those who will be. Companies spend thousands — even millions — of dollars installing antivirus, firewalls and other measures to protect networks and the confidential or proprietary information that resides on them.
What if the “hack” or data theft comes from the inside?
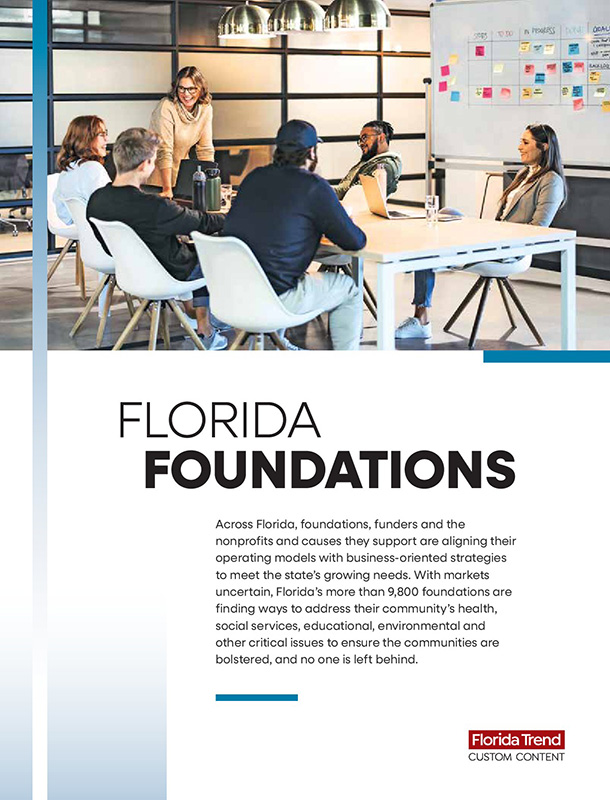
Theft of corporate trade secrets and proprietary content is on the rise. Some fear outside forces. Yet, threats posed by employees with network access to the most sensitive data are an often overlooked threat to intellectual property.
Business owners, CEOs, and HR and IT executives must understand these threats and take proactive, reasonable steps to safeguard the corporate IT network and the data stored there. By taking a layered approach, companies can protect their data — and prove they have exercised reasonable measures to safeguard their data.
Among the reasonable steps are …
Implement escalated password protection. Anyone who has access to the computer network — from the receptionist to employees on the factory floor to senior management — should be issued a unique password. Implement a hierarchical security protocol across the network to ensure certain employees or executives are granted access based on their seniority within the organization.
Regularly sign and update non-disclosure agreements. Upon hire, then at every annual review, employees should sign NDAs outlining that any information on the company server is company property.
Out the door? Shut it down. When an employee departs, IT must immediately disable their network access.
Conduct recurring digital forensics. Don’t wait for a suspected theft to inspect the network. Whether on-staff or a hired expert, a digital forensics specialist can regularly monitor the network or investigate suspicious downloads or data transfers.
Suspect theft? Take immediate action. If you find evidence of suspicious activity, seek an injunction for immediate return of the data and prohibiting any use.
In many cases of theft of trade secrets, courts want evidence that the data was protected content and that the company made every reasonable effort to protect the content in question.
Statutes like the Uniform Trade Secret Act and the Defend Trade Secret Act both may provide relief, even in the absence of signed NDAs. Statutes alone, however, are insufficient protection. Companies must take proactive measures to protect themselves from threats — including those that may walk in your door every day.
Paul O. Lopez is COO of Tripp Scott and chair of the firm’s Litigation Department. He focuses his practice on workplace and employment law, including shareholders disputes under Ch. 605 and Ch. 607 of the Florida Statutes.
Learn more at www.trippscott.com.